
DAGG and Pyth are pleased to announce our collaboration across several oracle integrations in DAGG v1.0 DEX Aggregator on Solana, the first of which is live on Solana Mainnet.
We selected Pyth’s SRM/RAY price oracle because it provides the highest quality price data, delivered by the largest and most decentralized group of independently run, Sybil-resistant oracles. Our users can also monitor the real-time health of the oracle via Pyth’s various monitoring resources, in order to gain insights into the oracle network as a whole, or the individual nodes and their on-chain responses.
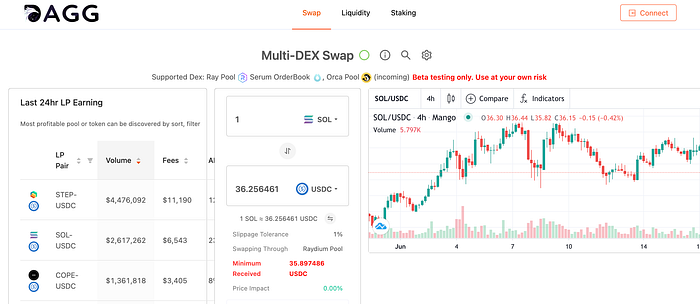
DAGG aggregator for splitting up trades to minimize slippage, is integrating the on-chain price from all of Pyth’s Price Reference Contracts into the UI. This will serve as the basis for calculating the USD value of user balances & token amounts.
About DAGG
DAGG aims to become the trading portal of Solana, and will realize a one-stop trading aggregation service of multiple DEX and DeFi protocols on Solana. It is set to offer the best DEX aggregator protocol specifically designed on the Solana blockchain.
The Solana DEX ecosystem is growing fast, and there are hundreds of teams building new DEXs, lending, and DeFi platforms on Solana. With our new cross-chain DEX aggregator protocol, we hope to bring the value of all these DEXs and DeFi protocols together in one easy-to-use platform. Above all else, the DAGG Trade DEX aggregator will provide enhanced liquidity for trading and a better all-around user experience.
About Pyth Netwok
Pyth Network is a next generation oracle solution designed to bring Hifi data to DeFi, it connects high-fidelity market data from the world’s largest professional traders and exchanges to any smart contract, anywhere.
Pyth Network is being built by some of the biggest names in traditional finance and DeFi with the goal of providing the infrastructure for DeFi to support substantial growth in the market. This requires legally authorized access to unique data sets, sub-second update speeds, sophisticated outputs and aggregation methods, and a thorough incentive system to ward off spurious or malicious data breaches.
Website: https://daggtrade.com/
Telegram: https://t.me/DAGGTrade
Discord: https://discord.gg/vV6rVZVF
Twitter: https://twitter.com/DaggTrade
Email: foundation@daggtrade.com
